The schema contains the definition for all the objects (example: user, computer and printers) in the directory. If we create an object in an active directory, it is validated against the corresponding object definition in the schema before being record to the directory. The schema is made up of classes and attributes. The default schema contains a set of object classes and attributes to meet our desired needs. Schema is extensible; we can modify and add attributes and classes to the base schema. Schema changes can affect the entire network. So before changing the schema, test in the lab environment.
Monday, March 28, 2011
Wednesday, March 23, 2011
FSMO - flexible single master operation - explained
Forest-wide roles
1) Schema Master
2) Domain naming master
Domain-Wide Roles
1) Relative Identifier master
2) PDC Emulator
3) Infrastructure Master
Schema master:
Schema master is a forest-wide operation master role because it contains the master list of objects classes and attributes that are used to create all active directory objects, for example users, computers and printers. Domain controller that holds the schema master role is the only domain controller that can perform write operation to the directory schema. The objects updates are replicated from the schema operation master to all other domain controller in the forest.
Domain Naming Master
Domain naming master is a forest-wide operation master role. It manages the addition or remove of all directory partition regardless of domain in the forest hierarchy. The domain naming master can perform the below operation.
"Add or remove-reference objects"
"Add or remove domains"
"Add or remove application directory partitions"
"Validate domain rename instructions"
Add or remove-reference objects
If we install Active directory, the first domain controller in a new forest, the schema, configuration and directory partition will create on the domain controller. At this time, a cross-reference object (class crossRef) will be created for each directory partition. A cross-reference object identifies the name and server location of each directory partition in the forest domain. If the domain naming master is not working, then we cannot add or remove cross-reference objects. Cross-reference object looks like (CN=partitions,CN=configuration,DC=forestrootdomain).
Add or Remove domains
Domain naming master has the authority to add a new domain. It manages this process preventing the multiple domains from joining the forest with the same domain name. During active directory installation to create or delete a child domain, it will contacts the domain naming master and request the add or remove process. It only responsible to ensure that domain names are unique.
Add or remove application directory partitions
Application directory partitions that can be created on domain controllers running windows server 2003 or later to provide LDAP storage for dynamic data. DNS creates and uses application directory partitions by default when it is installed in a forest with the domain controller that runs windows 2003 or later. DNS automatically created two default DNS application directory partition (ForestDnsZone & DomainDnsZones).
Validate domain rename instructions.
When we use the domain rename tool, random.exe, to rename domain. It should be able to access the domain naming master.
Relative Identifier master
RID master is a domain-wide operations master role. It only responsible for allocating the sequence of unique RIDs to each domain controller in its domain and all objects. It maintains a pool of RIDs to be used by domain controllers in its domain and providing group of RIDs to each domain controller when necessary. When we create a new domain controller is added to domain, the RID master allocates batch of approximately 500 RIDS from the domain RID pool to that domain controller. Whenever create a new security principal is created on the domain controller, the domain controller draws from its local pool of RIDs and assign to new object.
PDC Emulator
It acts as a Windows NT PDC in domains that contains client computers operating without AD client software or Windows NT backup domain controllers (BDC). In addition, the PDC emulator processes password changes from clients and replicates that updates to the Windows NT BDC. If logon authentication fails at another domain controller due to a bad password, that domain controller forwards the authentication request to the PDC emulator before rejecting the logon attempt.
Infrastructure Master
Infrastructure master responsible for updating object reference in its domain that point to the object in another domain. It updates object reference locally and uses replication to bring all other replicas of the domain up to date. The object reference contains the objects globally unique identifier (GUID), distinguished name and possibly a SID. The distinguished name and SID on the object reference are periodically updated to reflect changes made to the actual object.
Labels:
Active Directory
Tuesday, March 22, 2011
Operation Master and corresponding Directory Partition detail
If an FSMO role that has been taken offline is intentionally or unintentionally returned to services, it should replicate changes on the directory partition. The directory partitions maintain each operations master are defined in the following tabular column.
| Opearation Master Role | Directory Partition |
| Schema Master | Schema Partition |
| Domain Naming Master | Configuration Partition |
| PDC(Primary Domain Controller) emulator | Domain Partition for the operation master role owners domain |
| RID Master | Domain partition for the opearation master role owners doamin |
| Infrastructure Master | Domain partition for the opearation master role owners doamin |
Labels:
Active Directory
Friday, March 18, 2011
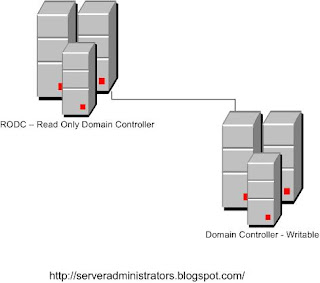
RODC – read only domain controller windows 2008
An RODC is an additional domain controller for a domain. It hosts read-only partition of the AD database. Only accept relocated changes to AD and never initiate replication. Replication uses only a one-way connection from domain controller that has a writable database copy to the read only domain controller (RODC). It mainly designed for branch office environment for physical security concern. It cannot hold operation master roles, can be deployed only on windows 2008 server core for additional security. The following RODC functionality extenuates these problems.
- Credential Cache
- Admin role separation
- Read only : Active directory – Domain Services Database
- Unidirectional replication
- Read only: DNS
Credential Cache:
RODC does not store user or computer credentials by default. It has exception for the computer account of the RODC and a special krbtgt account that each RODC has. We can explicitly allow any other credential caching on an RODC. It advertises as KDC (Key Distribution Center) for the branch office. It uses different krbtgt account and password than the KDC on the writable domain controller uses when it signs or encrypts ticket-granting request. If account is successfully authenticated, the RODC attempts to contact writable domain controller at the hub site and request a copy of the appropriate credentials, then writable domain controller recognizes that the request is coming from an RODC and consults the PRP (Password replication policy) in effect for the RODC. The password replication policy decides if a computer or user credentials it can be replicated from the writable domain controller to the Read only domain controller and RODC caches them. RODC after cached the credentials, it can directly give the service to user’s logon requests until the credentials change.
Admin role separation:
We can delegate local admin access for read only domain controller to any domain user, but that user can’t do administrative task on any other domain or domain controller. It permits only allow on RODC to perform administrative tasks.
Read only: Active directory – Domain Services Database:
RODC have the all the active directory objects and attributes that a writable domain controller holds, except account passwords. Active directory database changes cannot be made to RODC Active directory database. Changes must be made on a writable domain controller and then replicate to RODC.
Unidirectional replication
RODC is unidirectional replication because no changes are written directly to it and also no changes originate at the RODC. Unidirectional replication applies to both AD DS and Distributed File System Replication of SYSVOL. The RODC performs normal inbound replication for AD DS and SYSVOL changes.
Read only DNS
We can deploy DNS service on read only domain controller, it able to replicate all application partition that DNS uses. Client system can query it for name resolution as they query any other DNS server. It does not client updates directly.
Labels:
Windows 2008 Server
Tuesday, March 15, 2011
Windows 2008 Active Directory Replication Protocols
Replication is performed through replication transport protocols. Replications within a site perform by RPC-over-IP transport protocols. Replication between sites performs by two replication transport protocols IP – RPC over IP and SMTP over IP. Two different sites can replicate only with SMTP over IP. RPC replication between sites can be scheduled and compressed, within a site is not compressed.
SMTP, it enables low speed, asynchronous replication between the schema, configuration and global catalog partition, but not between domain directory partitions. SMTP traffic can be secured, monitor able and manageable across the environment
RPC over IP, it enables low speed, point-to-point, and synchronous replication between all directory partitions. RPC replication is synchronous, where SMTP replication is asynchronous. Bandwidth is limited; it is a disadvantage to enforce an entire transaction to complete before another can begin. In SMTP transaction can be process simultaneously, so each transaction is receiving some attention all the time.
To adjust the default size of the replication packet that active directory replication data, by can modify the registry value in the following key: HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\NTDS\Parameters.
RPC replication within a site:
Replicator intra site packet size (objects)
Range: >=1
Replicator intra site packet size (bytes)
Range: >=10 KB
Range: >=10 KB
For RPC replication between sites:
Replicator inter site packet size (objects)
Range: >=1
Range: >=1
Replicator inter site packet size (bytes)
Range: >=10 KB
Range: >=10 KB
For SMTP replication between sites:
Replicator async inter site packet size (objects)
Range: >=1
Range: >=1
Replicator async inter site packet size (bytes)
Range: >=10 KB
Range: >=10 KB
Labels:
Active Directory
Windows 2008 Active Directory replication features
· It partitioning of the data store and domain controllers in a domain hosts only the domain naming context for their domain. It helps keep replication to a minimum, particularly in mltidomain forests.
· It includes application directory partition and global catalog – partial set of attribute. By default, it not replicated to every domain controller in the forest.
· Within a single site, distinct control of intrasite replication and Intersite replication (between sites).
· It has features of collision detection and management. Although rare, that an attribute will have been modified on two different domain controllers during a single replication. In such a situation, the two changes will have to be reconciled. ADS have resolution algorithms’ that satisfy almost
all situations.
all situations.
· Attribute level of replication. If an object attribute is modified, only that attribute only will be replicate, the entire object is not replicated except when the new object is created.
· By default, Active directory will configure an effective the, two way replication topology. So that the loss of any one domain controller does not impact the replication. This topology automatically created when as domain controller are moved, added or moved between sites.
Labels:
Windows 2008 Server
Monday, March 14, 2011
Domain and Forest fucntional levels in Windows 2008 server:
| Domain Mode | Forest | Supported Domain Controller by Operating System |
| Windows 2008 Server | Windows 2008 Server | Windows 2008 Server |
| Windows 2000 native | Windows 2000 | Windows Server 2008,2003,2000 |
| Windows 2003 Server | Windows 2003 Server | Windows 2003 and 2008 Server |
In Windows Server 2008, forest and domain functionality provides a way to enable forest-wide or domain-wide features remove outdated backward compatibility within the environment, and improve Active Directory performance and security Active Directory features.Different levels of forest and domain functionality are available, depending on domain and forest functional level
When the first Windows Server 2008–based Domain Controller is deployed in a domain or forest, the domain or forest operates by default at the lowest functional level that is possible in that environment, meaning Windows 2000 Native Mode. This allows you to take advantage of the default Active Directory features while running versions of Windows earlier than Windows Server 2008. When you raise the functional level of a domain or forest, a set of advanced features becomes available.
After the domain functional level is raised, DCs that are running earlier operating systems cannot be introduced into the domain. For example, if you raise the domain functional level to Windows Server 2008, Domain Controllers that are running Windows Server 2003 cannot be added to that domain.
Unless you still have old NT 4.0 BDCs there's no reason for staying in Mixed Mode, and as you already know, Windows Server 2008 does not support NT 4.0 BDCs, so if you are still using them and planning to upgrade your Active Directory to Windows Server 2008, re-think your strategy.
As for Windows 2000 Native Mode, unless you still have Windows 2000 Domain Controllers, again, there's no reason for staying in that function level. However, if you still do, remember that Windows Server 2008 does only supports Windows 2000 SP4. Be sure to have SP4 on all your Windows 2000 DCs.
Note: Network clients can authenticate or access resources in the domain or forest without being affected by the Windows Server 2003 or Windows Server 2008 domain or forest functional levels. These levels only affect the way that domain controllers interact with each other. However, be aware of the fact that regardless of the domain or function level, servers running Windows NT Server 4.0 are NOT supported by domain controllers that are running Windows Server 2008, meaning you MUST have additional DCs running Windows 2000/2003 to support older NT 4.0 servers.
Domain Function Levels
To activate a new domain function level, all DCs in the domain must be running the right operating system. After this requirement is met, the administrator can raise the domain functional level. Here's a list of the available domain function levels available in Windows Server 2008:
Windows 2000 Native Mode
This is the default function level for new Windows Server 2008 Active Directory domains.
Supported Domain controllers – Windows 2000, Windows Server 2003, Windows Server 2008.
Features and benefits:
Group nesting – Unlike Windows NT 4.0, allows placing of a group of one scope as a member of another group of the same scope.
Universal security groups – Allows usage of Universal security type groups.
SidHistory – Enables usage of SidHistory when migrating objects between domains.
Converting groups between security groups and distribution groups – Unlike Windows NT 4.0, allows converting of a group type into another group type (with some limitations).
Windows Server 2003 Mode
To activate the new domain features, all domain controllers in the domain must be running Windows Server 2003. After this requirement is met, the administrator can raise the domain functional level to Windows Server 2003
Supported Domain controllers – Windows Server 2003, Windows Server 2008.
Features and benefits include all default Active Directory features, all features from the Windows 2000 native domain functional level, plus:
Universal group caching – Windows Server 2003 functional level supports Universal group caching which eliminate the need for local global catalog server.
Domain Controller rename – By using the NETDOM command.
Logon time stamp update – The lastLogonTimestamp attribute will be updated with the last logon time of the user or computer. This attribute is replicated within the domain.
Multivalued attribute replication improvements – Allows incremental membership changes, which in turn enables having more than 5000 members in a group and better replication capabilities.
Lingering objects (zombies) detection – Windows Server 2003 has the ability to detect zombies, or lingering objects.
AD-integrated DNS zones in application partitions – This allows storing of DNS data in AD application partition for more efficient replication.
Users and Computers containers can be redirected – This allows the redirection of the default location of new users and computers (by using the REDIRUSR and REDIRCMP commands).
Support for selective authentication – Makes it possible to specify the users and groups from a trusted forest who are allowed to authenticate to resource servers in a trusting forest.
Windows Server 2008 Mode
To activate the new domain features, all domain controllers in the domain must be running Windows Server 2008. After this requirement is met, the administrator can raise the domain functional level to Windows Server 2008.
Raising the domain and forest functional levels to Windows Server 2008 is a nonreversible task and prohibits the addition of Windows 2000–based or Windows Server 2003–based Domain Controllers to the environment. Any existing Windows 2000–based or Windows Server 2003–based Domain Controllers in the environment will no longer function, and in fact, the upgrading wizard will not allow you to continue with the operation. Before raising functional levels to take advantage of advanced Windows Server 2008 features, ensure that you will never need to install domain controllers running Windows 2000-based or Windows Server 2003–based Domain Controllers in your environment.
Supported Domain controllers – Windows Server 2008.
Features and benefits include all default Active Directory features, all features from the Windows Server 2003 domain functional level, plus:
Fine-grained password policies – Allows multiple password polices to be applied to different users in the same domain.
Read-Only Domain Controllers – Allows implementation of domain controllers that only host read-only copy of NTDS database.
Advanced Encryption Services – (AES 128 and 256) support for the Kerberos protocol.
Granular auditing – Allows history of object changes in Active Directory.
Distributed File System Replication (DFSR) – Allows SYSVOL to replicate using DFSR instead of older File Replication Service (FRS). It provides more robust and detailed replication of SYSVOL contents.
Last Interactive Logon Information – Displays the time of the last successful interactive logon for a user, from what workstation, and the number of failed logon attempts since the last logon.
Forest function levels
Forest functionality activates features across all the domains in your forest. To activate a new forest function level, all the domain in the forest must be running the right operating system and be set to the right domain function level. After this requirement is met, the administrator can raise the forest functional level. Here's a list of the available forest function levels available in Windows Server 2008:
Windows 2000 forest function level
This is the default setting for new Windows Server 2008 Active Directory forests.
Supported Domain controllers in all domains in the forest – Windows 2000, Windows Server 2003, Windows Server 2008.
Windows Server 2003 forest function level
To activate new forest-wide features, all domain controllers in the forest must be running Windows Server 2003. Read my "Raise Forest Function Level in Windows Server 2003 Active Directory" article for more info about that.
Supported Domain controllers in all domains in the forest – Windows Server 2003, Windows Server 2008.
Features and benefits include all default Active Directory features, plus the following features:
Forest trust.
Domain rename.
Linked-value replication – Changes in group membership to store and replicate values for individual members instead of replicating the entire membership as a single unit.
Deployment of an RODC.
Intersite topology generator (ISTG) improvements – Supports a more efficient ISTG algorithm allows support for extremely large numbers of sites.
The ability to create instances of the dynamicObject dynamic auxiliary class.
The ability to convert an inetOrgPerson object instance into a User object instance, and the reverse.
The ability to create instances of the new group types, called application basic groups and Lightweight Directory Access Protocol (LDAP) query groups, to support role-based authorization.
Deactivation and redefinition of attributes and classes in the schema
Labels:
Active Directory
Friday, March 11, 2011
Global catalog in active directory
Global catalog is a centralized and distributed data repository;
It contains searchable and partial representation of every object in every domain in the forest.
It stored on a domain controller, it has been designated as global catalog server and is distributed by
multimaster replication.
If we search the active directory objects that are redirected to the global catalog, because it is faster, it
does not involve referral to different domain controller.
It has ability to locate objects from any domain without having to know the domain name.
The global catalog updated and built automatically by active directory.
For optimize search, we can edit the schema by adding and removing attributes that are stored in global
catalog.
In single domain forest, global catalog server stores a full and writable replica of the domain. It does not
store partial data.
I will post more details in the upcoming articles.
Labels:
Active Directory
Wednesday, March 9, 2011
How to block Gmail on sonicwall firewall, not Google apps - solved
If you want to block Gmail on sonicwall firewall, most of the people try to add the urls. But it won’t block, because it block domain only. If you want allow Google apps and block gmail. Better need to add keyword /mail in the keyword blocking. For more info refer this link Block gmail Sonicwall
Labels:
TIPS and Tricks
Tuesday, March 8, 2011
Windows Deployment Services – Changes from RIS (Remote Installation Services)
RIS is a predecessor of windows deployment services. It has some of lot improvements in this version.
I) Here GUI that allows us to select and deploy images and to mange windows deployment services server and clients.
II) It has higher performing and extensible PXE server.
III) It can transfer data and images by using multicast namespace on a standalone server.
IV) A new boot menu format for selecting the boot images.
V) It can transfer data and images by using multicast transmission.
VI) It can deploy windows 2008 and vista operating system. Windows PE is the boot OS, it uses image based installation using .wim file.
Labels:
Windows Deployment Services
Windows Deployment services – Server functionalities (windows 2003):-
In windows Deployment services there are three server modes (roles). These modes determine the image format, boot environment and administration experience. To check the operating mode in WDS, from the command prompt WDSUTIL /get-server /show:config , above command output displays the server mode(role).
Native Mode:
In native mode we can deploy only .wim images only. To enable native mode, install and configure WDS on a server that has RIS Installed but should not configure it. If already configured need to uninstall and reinstall before configuring windows deployment services.
Legacy Mode:
Legacy mode environment used generally, if you do not have windows vista in the environment. For this mode install and configure RIS and then install Windows deployment services (but should not configure).
Mixed Mode:
In Mixed mode environment we can deploy RISETUP and RIPREP images type using OSChooser and also can deploy .wim based images by using WDS management tools. For mixed configuration, configure Windows deployment services on existing RIS configuration.
Labels:
Windows Deployment Services
Monday, March 7, 2011
Advantages of Windows Deployment Services
I) It allows network based installation of operating systems, include also windows vista and windows server 2008.
II) We can deploy windows images to computers without operating system.
III) It reduces the complexity of deployment and cost with inefficient manual installation.
IV) It provides end-to-end solution for deployment of operating system to client computers and servers
V) It uses standard windows 2008 server setup technology, includes WIN PE, image based and .wim files
VI) It also support mixed environment that includes Windows XP, 2003 and 2008.
Labels:
Windows Deployment Services
Windows Deployment Services Components - Windows 2008 Server
There are three components are available in windows deployment services.
· Server Components
· Client Components
· Management Components
Server Components:
PXE – Prexecution environment
TFTP – (Trivial file transfer protocol)
Both the server components for network booting a client to load and install an operating system, shared folder and image repository. It contains boot images, files and install images, it need specifically for network booting.
Client Components:
Client components includes graphical user interface – windows pre-installation environment (Windows PE) this component to communicate with the server components to install the image.
Management Component:
The set of tools that used to manage the server, operating system image and client computer accounts.
Labels:
Windows Deployment Services
Thursday, March 3, 2011
VB Script to unlock user accounts - Active directory
The below VB script code can unlock the user accounts in active directory .Copy the below code and paste to notepad and save it as .vbs extension.
UserName = InputBox("Enter the user's login name that you want to unlock:")
DomainName = InputBox("Enter the domain name in which the user account exists:")
Set UserObj = GetObject("WinNT://"& DomainName &"/"& UserName &"")
If UserObj.IsAccountLocked = -1 then UserObj.IsAccountLocked = 0
UserObj.SetInfo
If err.number = 0 Then
Wscript.Echo "The Account Unlock Failed. Check that the account is, in fact, locked-out."
Else
Wscript.Echo "The Account Unlock was Successful"
End if
UserName = InputBox("Enter the user's login name that you want to unlock:")
DomainName = InputBox("Enter the domain name in which the user account exists:")
Set UserObj = GetObject("WinNT://"& DomainName &"/"& UserName &"")
If UserObj.IsAccountLocked = -1 then UserObj.IsAccountLocked = 0
UserObj.SetInfo
If err.number = 0 Then
Wscript.Echo "The Account Unlock Failed. Check that the account is, in fact, locked-out."
Else
Wscript.Echo "The Account Unlock was Successful"
End if
Labels:
Scripts
Script to view disk free space
The below simple VB Script to show the free disk space in the local computer, copy the below code and paste to notepad and save it as .vbs extension.
Const HDD = 3
strComputer = "."
Set objWMIService = GetObject("winmgmts:" _
& "{impersonationLevel=impersonate}!\\" & strComputer & "\root\cimv2")
Set colDisks = objWMIService.ExecQuery _
("Select * from Win32_LogicalDisk Where DriveType = " & HDD & "")
For Each objDisk in colDisks
Wscript.Echo "Drive: "& vbTab & objDisk.DeviceID & vbTab & objDisk.FreeSpace
Next
Labels:
Scripts
Wednesday, March 2, 2011
WDS - Windows Deployment Services installation requirements
DHCP
A Windows deployment service uses PXE (preboot execution environment). So we must have working DHCP server with an active scope. DHCP option 66 and 67 need to add on server. Option 66 set to the windows deployment services server and option 67 should be set to boot\x86\wdsnbp.com
NTFS Partition
NTFS partition requires for storing the operating system images.
Active Directory
Windows deployment services server must be either domain controller for an active directory domain or member of an active directory domain. It supports all domain and forest configuration.
DNS
DNS server on the network requires to running windows deployment services.
Note:-
RIS (Remote installation services) must be installed on windows server SP1 or SP2 version. But no need to configure it.
Labels:
Windows Deployment Services
WDS – Windows Deployment Services – Definition
I) WDS is the united, updated and redesigned version of Automated Deployment Services (ADS) and Remote Installation Services (RIA)
II) Through WDS, we can deploy windows XP, Vista, Server 2003, 2008 and service pack also.
III) It fully customized and automated through the use of unattended installation scripting files.
IV) We can do naming the machine, having the machine to join a domain.
V) In Windows 2008 version of WDS, supports IP multicast deployments. It allows new clients to join an existing deployment that has already started.
VI) WDS multicast uses the IGMP protocol.
VII) It also supports x64-computer with (EFI) Extensible firmware interface.
VIII) Windows PE is used to boot the operating System
IX) WDS included on Windows 2003 SP2, In Windows 2008 have inbuilt with more features.
X) WAIK (Windows Automated Installation Kit) tools are used to build the operating system image. Windows Imaging Format (WIM) is the OS image format.
Labels:
Windows Deployment Services
Tuesday, March 1, 2011
Recover Formatted drive
I had recently infected virus my hard drive, the files were deleted. i have used a tool to recover the data, thats free license. here i would like to refer the link. http://www.piriform.com/recuva
Labels:
TIPS and Tricks
Subscribe to:
Posts (Atom)